Ensuring the Security of Your Network-Attached Storage: Best Practices for Home and Business
Asenqua Tech is reader-supported. When you buy through links on our site, we may earn an affiliate commission.
Key Takeaways:
- Exercising stringent protective measures for NAS is essential to safeguard sensitive data against unauthorized access.
- Comprehending and navigating the landscape of NAS-related threats enables more informed and effective defense strategies.
- Regular maintenance of NAS systems, including software updates and user training, is pivotal in maintaining security integrity.
Introduction to Network-Attached Storage Security
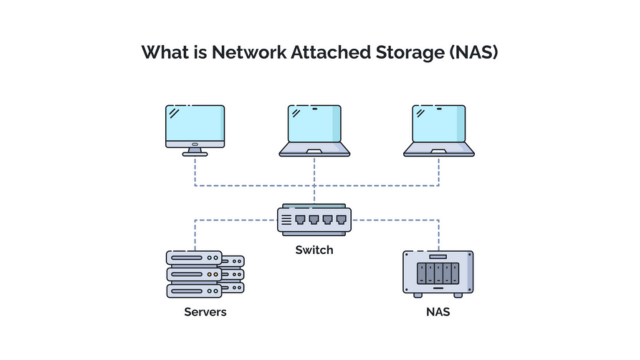
In our ever-growing digital age, the proliferation of data has necessitated efficient storage solutions that can be accessed from multiple points within a network. This has led to the increased adoption of Network-Attached Storage (NAS) devices for both personal and professional use. These dedicated file storage systems facilitate data sharing and provide streamlined storage capabilities. Yet, despite their convenience and benefits, NAS systems are not immune to security threats and require adequate protection. The vulnerability of these systems to cyber-attacks, data corruption, and unauthorized access underlines the necessity of robust NAS security protocols. It’s not just about keeping your data handy; it’s about keeping it out of harm’s way.
Understanding NAS Security Challenges
With the convenience of NAS, there also comes an increased risk of digital threats. NAS systems often become targets for cybercriminals due to the valuable data they store. The vulnerabilities inherent in networked devices can be exploited to gain unauthorized access, launch malware attacks, or even infiltrate a network. A deeper understanding of these challenges and education on the various forms of NAS attacks is crucial for anyone securing these devices. In this Internet of Things era, where interconnectedness is the norm, recognizing the potential ingress points for security threats is the cornerstone of an effective NAS security strategy.
Strengthening Your NAS with Robust Security Measures
Securing a NAS system involves multiple layers of defense, starting with the fundamental step of employing complex passwords and changing them regularly. However, a strong security posture goes beyond just passwords; it includes a comprehensive audit of user permissions, network settings, and the physical security of NAS devices. Implementing robust encryption practices and using trusted security software are essential to protect the data stored within NAS systems. Incorporating two-factor authentication, intrusion detection systems, and regular reviews of security logs further fortify the NAS against unauthorized access or malicious attacks.
Implementing Access Control Strategies
Access control is integral to network security, ensuring only authorized users can access your NAS. A foundational aspect is the principle of least privilege, which stipulates granting users only the level of access necessary for their roles. It takes constant attention and adjustment to manage permissions rigorously and precisely in response to changing needs and possible threats. A vital part of this process includes:
- Implementing user authentication mechanisms.
- Robust access control lists (ACLs).
- Considering the use of network-attached storage security tools designed to prevent unauthorized access.
The Significance of Regular Software Updates
The importance of regularly updating the NAS firmware must be balanced, as failing to do so leaves the system susceptible to exploitation via known vulnerabilities. Manufacturers of NAS devices frequently release software patches and updates not only to improve functionality but also to mitigate newly discovered security risks. Prompt application of these updates is an essential habit that users and administrators must develop. By automating this process, if feasible within the NAS environment, one can ensure consistency in applying these critical updates without significant manual oversight.
Advanced Security Protocols for NAS
As cyber threats become more sophisticated, so must the security measures protecting NAS systems. Advanced security protocols may include VPNs (Virtual Private Networks) for secure remote access and SSL/TLS (Secure Socket Layer/Transport Layer Security) protocols for encrypting data in transit. Enabling IP filtering or MAC address filtering also adds a layer of protection, ensuring that only trusted devices can communicate with the NAS. Integrating comprehensive virus and malware protection into the NAS ecosystem can be a powerful deterrent against the ever-growing wave of cyber threats.
Network Configuration and Segmentation
Designing a well-structured network that involves segmenting the NAS can significantly enhance security. Organizations can restrict possible invaders’ reach and mitigate the impact of any unwanted access by dividing sensitive data into distinct physical subnetworks or by establishing VLANs (Virtual Local Area Networks). With these precautions, other segments remain protected even if part of the network is compromised. This division assists in managing traffic and access rights and provides organized and secure data accessibility across different departments or user groups.
Backup Strategies to Counteract Data Loss
Backups are an indispensable element of a sound NAS security strategy, serving as a lifeline in the face of data loss scenarios. The 3-2-1 backup rule includes keeping three copies of your data, with two local but on different devices and one off-site, which is a widely advocated strategy for ensuring data redundancy and recoverability. Regularly scheduled backups and their subsequent verification can mitigate the repercussions of ransomware attacks or catastrophic hardware failures. Implementing snapshot technologies enables quick restoration to a secure state, reinforcing data resilience.
Monitoring and Auditing NAS Activity
Ongoing monitoring and auditing are vital to any NAS security plan. The continuous analysis of system logs helps detect abnormal activities that could indicate a security incident early. Systems for managing security information and events, or SIEMs, can give administrators a thorough picture of network activity and help them react quickly to threats.
Auditing your NAS also means periodically reassessing the access rights and verifying the effectiveness of the security controls, ensuring that the NAS remains a secure asset within the organizational infrastructure.
Training and Awareness: A Critical Security Layer
While technical measures are indispensable in securing a NAS, the human element must be considered. Creating a culture of awareness among users is essential for ensuring the safe handling of data. Regular training sessions to acquaint users with security best practices and new threats, alongside ongoing reminders about the importance of security hygiene, can dramatically reduce the risk of user error leading to security breaches. Empowering users through education transforms them from a potential liability into a formidable first line of defense against cyber threats. Staying abreast of the latest NAS security updates equips everyone involved with the tools and knowledge necessary to safeguard their data proactively.